PwnWinds: A Real-World Threat or Script-Kiddie Legend?
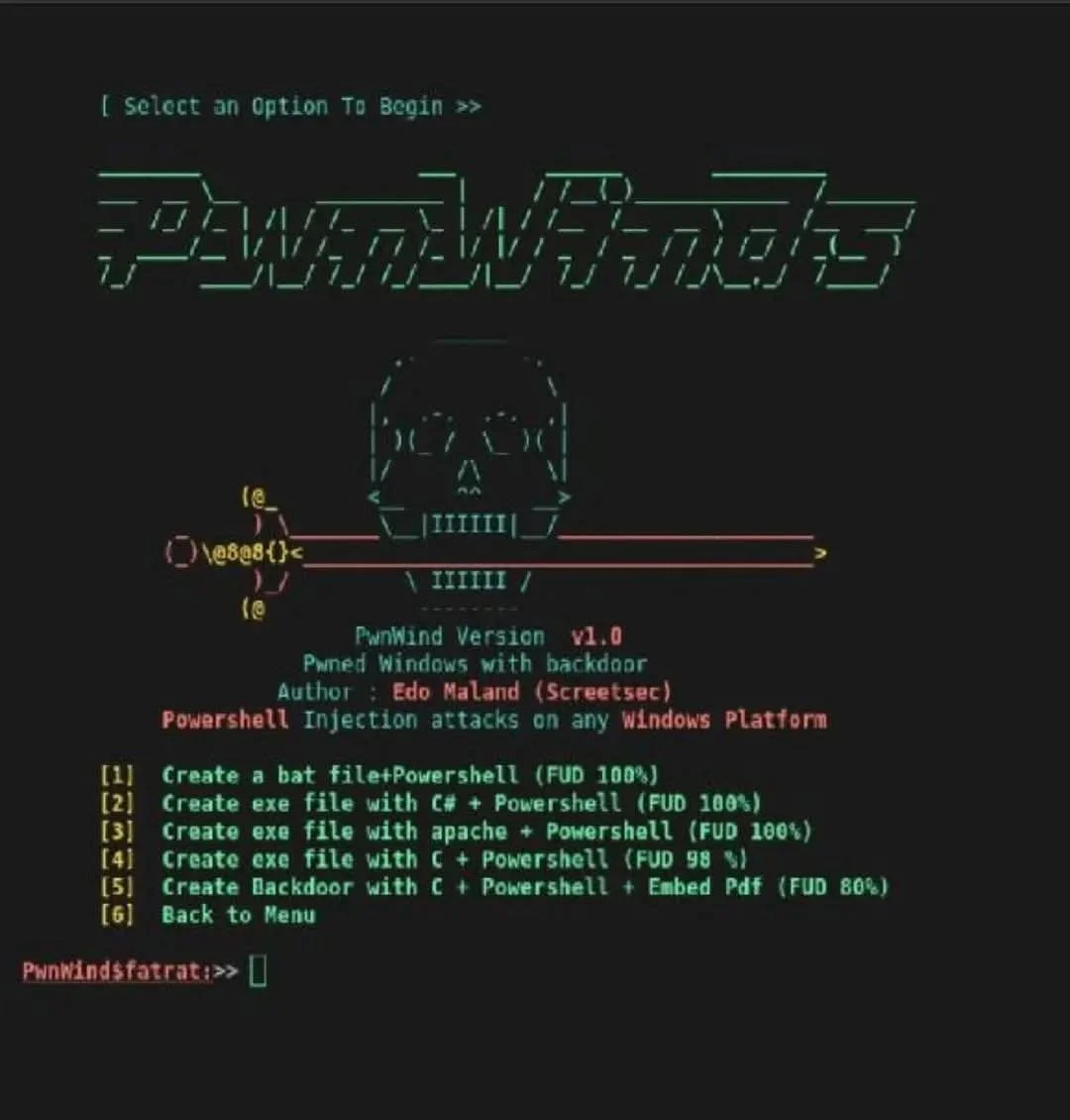
This image features PwnWinds v1.0, a specific module within a well-known hacking toolkit called TheFatRat. Developed by Edo Maland (who uses the handle Screetsec), PwnWinds is designed to generate backdoors specifically for Windows platforms.
While it might look like something out of a movie, its viability in today’s high-security landscape is a mix of legitimate threat and outdated marketing.
The Details: What Is PwnWinds?
PwnWinds is a script that automates the creation of malicious payloads. It primarily focuses on PowerShell Injection attacks, which are dangerous because they use a legitimate, built-in Windows tool (PowerShell) to execute malicious code, making it harder for basic antivirus software to detect.
The interface offers several "FUD" (Fully Undetectable) options:
FUD 100%: The tool claims these payloads (like .bat or .exe files) will bypass all antivirus scanners.
Multiple Vectors: It can embed payloads into C#, Apache-related files, or even PDFs to trick users into opening them.
MSFVenom Integration: Under the hood, it often relies on Metasploit's msfvenom to generate the actual malicious code, essentially acting as a simplified "wrapper" for more complex tools.
The Reality Check: Is It Actually Viable?
In the cybersecurity world, "100% FUD" is a bold claim that rarely stays true for long.
The "Cat and Mouse" Game: While a new version might bypass detection for a few days, security companies (like CrowdStrike or Microsoft) quickly update their signatures. Modern EDR (Endpoint Detection and Response) systems look for behavior (like a PDF suddenly launching PowerShell) rather than just a file's signature.
The Script-Kiddie Reputation: Tools like TheFatRat and PwnWinds are popular among "script kiddies"—novices who use pre-made scripts without understanding the underlying code. This makes them easy for professional Blue Teams (defenders) to spot because the "fingerprints" of these tools are well-documented.
Dependency Issues: As seen in developer forums, the tool is prone to breaking due to Python version conflicts or missing dependencies like Metasploit, making it less "plug-and-play" than it appears.
Influence on Cyber Warfare
Tools like PwnWinds represent the "democratization" of cyberattacks, lowering the bar for entry.
Offensive Influence
Rapid Deployment: It allows attackers to quickly generate and test different payload types without needing deep coding knowledge, fitting into the "low-effort, high-volume" attack strategy.
Social Engineering: By masking payloads in PDFs or .bat files, it provides an easy "delivery vehicle" for phishing campaigns targeting unsuspecting employees.
Defensive Influence
Signaling and Signatures: Because this tool is open-source and widely known, it serves as excellent "practice" for defenders. Security teams use the output of tools like PwnWinds to refine their detection rules.
Focus on PowerShell Security: The existence of PwnWinds has pushed organizations to tighten PowerShell security, such as using Constrained Language Mode or logging every command executed (Script Block Logging) to catch injection attempts in real-time.
The Sec Guy’s Verdict
PwnWinds isn't a "magic wand" for hackers, but it's a reminder that PowerShell remains a primary battleground. While its "100% FUD" claims are likely exaggerated against modern enterprise defenses, it remains a viable threat against unpatched systems or home users with basic antivirus.